Risks can be of two types—high threat or low threat. Likewise, some risks require a detailed mitigation plan while some risks do not involve any major planning. Whatever the case may be, risks must be identified as early as possible to have a lesser impact on the project.
Identification of risks forms the basis for the risk management process. It is an ongoing process as new risks may be developed at any stage of a project. Therefore, it should have a clear path to finding out new risks from time to time.
Table of Content
Project Risk Categories
In an IT project, there are five major project risks categories, which are:
Schedule Risks
Every project has a defined schedule. However, due to several reasons, such as wrong estimation at the initial stage or unavailability of resources, etc., the schedule may get impacted, which, in turn, can lead to unnecessary delay in project completion or an increase in project costs.
Budget Risks
Budget risks occur due to the wrong estimation of the project budget, overrunning of the cost, and the unexpected expansion of the project.
Operational Risks
These risks occur due to various events, like the failure of any process, lack of resources, issues in implementing processes, lack of communication among team members, a mismatch between the project plan and project execution, etc.
Technical Risks
Technical risks occur due to the failure of any functionality of the project. It also occurs due to the complexity of achieving the target, complex project modules, or any other issues in the technical aspect of the project.
Programmatic Risks
Programmatic risks are unexpected ones that cannot be determined in advance. The causes for these risks are external factors, like a shortage of funds planned, a present market scenario not matching the product, any rule amendment by the government, or any new expectation received from the client. These risks are taken care of at that time only when they arise.
Risks in an IT project can come up at any stage, in any shape, or of any size. Therefore, risk identification starts from the project initiation stage and continues throughout the entire life cycle of the project. However, it is the responsibility of a project manager to decide whether the risks can be avoided as per the situation or should be treated seriously.
New strategies are developed from time to time to manage these risks, resulting in a new plan for the project in terms of budget, schedule, resources, etc. However, the measures to deal with the risks are already planned in the initial stages of the project.
Factors Help in Identifying Project Risks
- Risk Management Plan
- Activity Cost and Activity Duration Estimates
- Stakeholder Register
- Organizational Process Assets
Risk Management Plan
It is one of the key inputs of the risk identification process. It describes the methods of risk identification, the requirements for risk analysis, and the overall management of the risk management framework.
Activity Cost and Activity Duration Estimates
These estimates help in understanding the project schedule and budget, which are considered to be one of the risk areas of a project. Thus, activity cost and activity duration estimates should be examined carefully to determine latent risks that lie within them.
Stakeholder Register
A stakeholder is an individual/group/organization who has a bearing on the outcome of a project either directly or indirectly. A stakeholder register includes information about all stakeholders involved in the risk identification process.
Organizational Process Assets
These assets include guidelines, policies or procedures of risk management, historical information or databases, and experience with previous similar projects. All these assets help in determining risks that may come up during a project.
Tools and Techniques used in Project Risk Identification Process
Some important tools and techniques used in the risk identification process are:
- Documentation Review
- Information-collection Techniques
- Brainstorming
- Delphi Technique
- Checklist Analysis
- Diagramming Techniques
Documentation Review
It involves examining various baseline documents that provide an idea of the ideal project execution path. This helps in ensuring the validity of assumptions and checking the constraints as they may alter the baseline estimates.
Information-collection Techniques
These include techniques, such as brainstorming, the Delphi technique, interviewing, and root cause analysis.
Brainstorming
It is a method of collecting ideas and viewpoints from different stakeholders of a project. The brainstorming approach needs not to be confined to the project team alone; it can be extended to the external subject matter experts, customers, and other stakeholders too.
They may also have a view on the project status or execution that can be vital in the risk identification process. The idea behind this exercise should be to get as many suggestions and opinions as possible and then apply appropriate filters to check what is useful in risk identification.
Delphi Technique
It is a method of holding anonymous interviews with experts about foreseeable risks. The results of the interviews are collated and studied by an independent team. The purpose of keeping interviews anonymous is to avoid confirmation bias or being influenced by other experts. Thus, experts share their thoughts solely based on their risk assessment.
There can be multiple rounds of anonymous discussions until a consensus or some trend on project risks emerges. Experts provide their views on different aspects of a project, such as cost, budget, etc. Based on the discussion, the project is executed or stopped.
Checklist Analysis
It is one of the simplest techniques to comply with standard processes and check any deviation-causing risks. It is more useful in projects involving some standard operations. For example, assembly lines work in a manufacturing or construction project. Not following checklists may lead to adverse situations and put the project at significant risk.
Diagramming Techniques
Many diagramming techniques help in the identification of risks. Some of them are explained as follows:
- Ishikawa Diagram: This is also called the cause-effect diagram or fishbone diagram. It lists the top causes of a particular defect. The root cause provides insight into potential risks.
- Flowchart: System or process flowcharts provide a visual depiction of the overall process and the relation between various components. Such visual representation helps in identifying the system or process gaps or points out failures quickly.
- Influence Diagram: An influence diagram depicts the decision-making flow. It identifies all elements, decisions, and objectives of a project and determines how various factors influence each other. Potential risks in the decision-making process can be identified from these diagrams.
The funding of projects is dependent on various factors, such as market health, economy, education, and jobs. In addition, all these factors influence each other.
The final output of this process is the risk register. The risk register records the results of risk analysis and response planning. This register also records the outcomes of other risk management processes. There are two major components of the risk register which include the list of all identified risks and the list of potential responses.
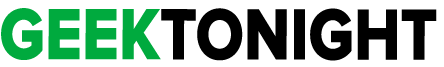
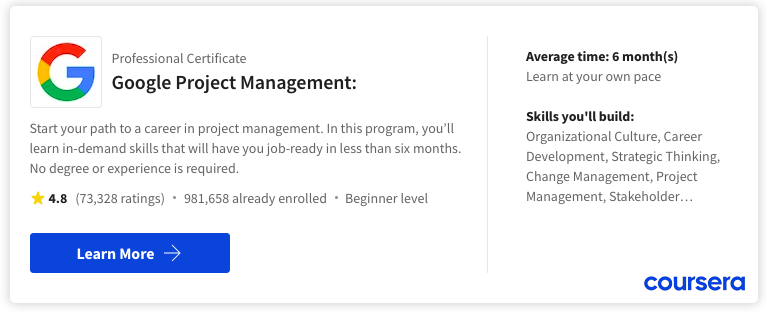
Best Project Management Courses
Project management skills are in demand. If you are ready to get started, consider enrolling in the Google Project Management: Professional Certificate Learn the job-ready essentials of project management in six months or less, such as initiating projects, risk management and change management. Also we have made list of best project management courses as there are a plethora of options available, and it can be challenging to identify the best one.
Best Project Management Tool
Best for:
- Mid & Large Size Team
- Higher Plan
- Standard Feature
- Flexible Database & Stability
Best for:
- Small & Growing Team
- Smaller Plan
- Standout Feature
- Try New Feature
The ideal project management tool selection will eventually rely on the particular requirements of your team. We suggest experimenting with the free versions of various tools to gauge your team’s comfort level and then proceeding accordingly.
Project Management Tutorial
(Click on Topic to Read)
- What is Project Management?
- Functions of Project Management
- What is Project?
- Project Managers
- What is Project Life Cycle?
- Project Feasibility Study
- What is Project Analysis?
- What is Project Planning?
- What is Project Selection?
- What is Project Schedule?
- What is Project Budget?
- What is Project Risk Management?
- What is Project Control?
- Project Management Body of Knowledge (PMBOK)
- Best Project Management Tools
- What is Project Organisation?
- What is Project Contract?
- Types of Cost Estimates
- What is Project Execution Plan?
- Work Breakdown Structure (WBS)
- Project Scope Management
- Project Scheduling Tools and Techniques
- Project Risk Identification
- Risk Monitoring
- Allocating Scarce Resources in IT Project
- Goldratt’s Critical Chain
- Communication in Project Management | Case Study
- Plan Monitor Control Cycle in Project Management
- Reporting in Project Management
- IT Project Quality Plan
- Project Outsourcing of Software Development
- Implementation Plan of Software Project
- What is Project Implementation?
- What is Project Closure?
- What is Project Evaluation?
- Software Project Management Challenges
- What is Project Management Office (PMO)?
- IT Project Team
- Business Case in IT Project Life Cycle
- PMP Study Guide